 Cybercriminals created the malware which is also known as DNSChanger, so that they can redirect internet traffic by hijacking the domain name systems o web browsers. This virus was discovered in 2007 which was shut down in 2011 by the US Federal Bureau of Investigation (FBI), Estonian police and other law enforcement agencies. The virus controlled so much web traffic for which a court order was obtained by the authorities to allow the FBI to operate replacement servers which allowed the traffic to flow normally.
Cybercriminals created the malware which is also known as DNSChanger, so that they can redirect internet traffic by hijacking the domain name systems o web browsers. This virus was discovered in 2007 which was shut down in 2011 by the US Federal Bureau of Investigation (FBI), Estonian police and other law enforcement agencies. The virus controlled so much web traffic for which a court order was obtained by the authorities to allow the FBI to operate replacement servers which allowed the traffic to flow normally.
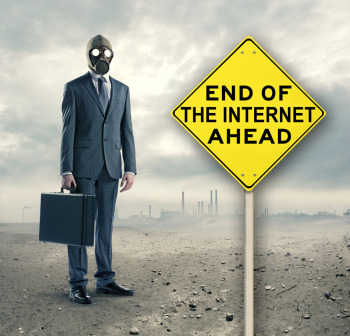
The order would expire on Monday, July 9 and it was reported by the experts that the infected computers would face an “internet doomsday”. More than 300,000 computers remained infected since June 11 according to a working group set by experts. Australia, Italy, Germany, India, Britain, Canada, France and U.S. are believed to be the countries where most of the computers are infected. Approximately 6000 Australian computer users would be affected by the DNSChanger malware and would have no internet from 1400 AEST on July 9, reported by the Australian Communications and Media Authority on Friday.
The Google, Facebook, FBI, internet service providers and security firms have been warning the users about the problem and directing them to fixes. Australians could check their computer is affected by going to http://dns-ok.gov.au/
Johannes Ullrich, a researcher with the SANS Security Institute said, “Reaching victims is a very hard problem, and something we have had issues with for years.”
It was said by IID chief executive Lars Harvey, “DNSChanger is an insidious form of malware affecting everyone from the everyday consumer to a large chunk of the Fortune 500.” He said the malware also compromises computers by preventing antivirus software updates.

Be the first to comment