
This article was last updated on April 16, 2022
Canada: ![]() Oye! Times readers Get FREE $30 to spend on Amazon, Walmart…
Oye! Times readers Get FREE $30 to spend on Amazon, Walmart…
USA: ![]() Oye! Times readers Get FREE $30 to spend on Amazon, Walmart…
Oye! Times readers Get FREE $30 to spend on Amazon, Walmart…
While I posted on this subject last year, the fact that it got almost no traction in the Western/American media is quite telling. Given the ongoing and rather tiresome Russophobia that makes headline news day after day after day and Donald Trumps recent comments on America’s intelligence network, I thought that the subject was worth repeating.
In early March 2017, WikiLeaks began to publish a massive treasure trove of documents that appeared to be CIA spying secrets, a set of documents whose authenticity was never denied by America’s chief spy agencies. In total, the first full part of the series, termed Year Zero by WikiLeaks, 8761 documents and files were released from inside the CIA’s Center for Cyber Intelligence located in Langley, Virginia. Here’s quote about the documents from the WikiLeaks May 7, 2017 press release:
“Recently, the CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized “zero day” exploits, malware remote control systems and associated documentation. This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA. The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.
“Year Zero” introduces the scope and direction of the CIA’s global covert hacking program, its malware arsenal and dozens of “zero day” weaponized exploits against a wide range of U.S. and European company products, include Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones.
Since 2001 the CIA has gained political and budgetary preeminence over the U.S. National Security Agency (NSA). The CIA found itself building not just its now infamous drone fleet, but a very different type of covert, globe-spanning force — its own substantial fleet of hackers. The agency’s hacking division freed it from having to disclose its often controversial operations to the NSA (its primary bureaucratic rival) in order to draw on the NSA’s hacking capacities.
By the end of 2016, the CIA’s hacking division, which formally falls under the agency’s Center for Cyber Intelligence (CCI), had over 5000 registered users and had produced more than a thousand hacking systems, trojans, viruses, and other “weaponized” malware. Such is the scale of the CIA’s undertaking that by 2016, its hackers had utilized more code than that used to run Facebook. The CIA had created, in effect, its “own NSA” with even less accountability and without publicly answering the question as to whether such a massive budgetary spend on duplicating the capacities of a rival agency could be justified.
In a statement to WikiLeaks the source details policy questions that they say urgently need to be debated in public, including whether the CIA’s hacking capabilities exceed its mandated powers and the problem of public oversight of the agency. The source wishes to initiate a public debate about the security, creation, use, proliferation and democratic control of cyberweapons.”
With Washington’s anti-Russia, anti-China, anti-North Korea and anti-Iran narratives in mind, let’s look in some detail at one of the CIA’s tools; obfuscation. Let’s look at a definition of obfuscation before we go any further:
“To obfuscate something means to throw something into shadow, make obscure, or to make it unclear or confusing.”
Here is how obfuscation is used in software development:
“The code obfuscation is a mechanism for hiding the original algorithm, data structures or the logic of the code, or to harden or protect the code (which is considered as intellectual property of the software writer) from the unauthorized reverse engineering process. In general, code obfuscation involves hiding a program’s implementation details from an adversary, i.e. transforming the program into a semantically equivalent (same computational effect) program, which is much harder to understand for an attacker.”
In case you were interested, here is a link to an entire paper on code obfuscation. Here is a more detailed look at how malicious code obfuscation can be used:
“All of these techniques can be used separately or in combination to obfuscate code, however for those scripting malware, code obfuscation greatly enhances two imperatives: the malware must evade detection, and survive long enough to complete its tasks. In order to do so it must:
1.) Ensure entry point obfuscation – hiding the initial security breach on the host machine or system by inserting code at an unlikely point in the infected file
2.) Resist manual and automated analysis – conceal suspicious signatures or behaviour
3.) Obfuscate the communication of instructions between the malware and the command and control server
4.) Ensure information exfiltration – hide what data has been compromised and where it was sent”
With that in mind, let’s look at the CIA’s Marble Framework which was released by WikiLeaks on March 31, 2017. This release contained 676 source code files for the CIA’s secret anti-forensic Marble Framework. Here’s a summary of Marble’s operations from WikiLeaks:
“Marble is used to hamper forensic investigators and anti-virus companies from attributing viruses, trojans and hacking attacks to the CIA.”
Marble does this by hiding (“obfuscating”) text fragments used in CIA malware from visual inspection. This is the digital equivalent of a specalized CIA tool to place covers over the english language text on U.S. produced weapons systems before giving them to insurgents secretly backed by the CIA.
Marble forms part of the CIA’s anti-forensics approach and the CIA’s Core Library of malware code. It is “[D]esigned to allow for flexible and easy-to-use obfuscation” as “string obfuscation algorithms (especially those that are unique) are often used to link malware to a specific developer or development shop.”
The Marble source code also includes a deobfuscator to reverse CIA text obfuscation. Combined with the revealed obfuscation techniques, a pattern or signature emerges which can assist forensic investigators attribute previous hacking attacks and viruses to the CIA. Marble was in use at the CIA during 2016. It reached 1.0 in 2015.”
Let’s look at some terminology for the Marble Framework:
Marble: A Marble is a specific algorithm that scrambles and unscrambles data.
Mibster: The Mibster is the utility that does the scrambling and altering of source files. The Mibster starts by choosing a Marble (an algorithm) from the filtered list of available algroithms. The Mibster then scans the directories containing source, looking for strings and data to scramble. The Mibster keeps a clean copy of the original source and replaces it with the scrambled versions of strings/data as well as supplies the unscramble function. The source should compile after Mibster modifies source.
Mender: The Mender restores the source files to their original state. If, for any reason, the Mibster fails or breaks the code, the Meder can always restore the state to its original.
Warble: A Warble is a wide-character string (wchar_t *) that needs to be scrambled by the Mibster.
Carble: A Carble is a multi-byte string (char *) that needs to be scrambled by the Mibster.
Validator: The Validator is a utility that takes (as an input) the receipt file generated by the Mibster. The Validator uses the receipt file to verify that all the strings intended to be scrambled are not contained in the final binary.
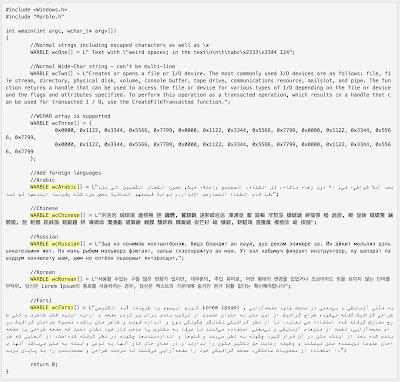
Now, let’s look at how nefarious the CIA is with its use of Marble. Here is a screen capture from the Marble Framework outline that was classified Secret/NoForn (no foreign governments):
Notice that the Warble (the character string that is scrambled by the Mibster utility which scrambles the source files) comes in five additional foreign languages; Arabic, Chinese, Russian, Korean and Farsi, languages that are spoken by the Axis of Evil nations as well as nations that the United States is not particularly playing well with.
Here’s another quote from WikiLeaks:
“The source code shows that Marble has test examples not just in English but also in Chinese, Russian, Korean, Arabic and Farsi. This would permit a forensic attribution double game, for example by pretending that the spoken language of the malware creator was not American English, but Chinese, but then showing attempts to conceal the use of Chinese, drawing forensic investigators even more strongly to the wrong conclusion, — but there are other possibilities, such as hiding fake error messages.”
Here is a link to the CIA’s PowerPoint presentation for the Marble Framework should you happen to be interested.
Let’s close with this quote from WikiLeaks:
“Once a single cyber ‘weapon’ is ‘loose’ it can spread around the world in seconds, to be used by rival states, cyber mafia and teenage hackers alike….
Cyber ‘weapons’ are not possible to keep under effective control.
While nuclear proliferation has been restrained by the enormous costs and visible infrastructure involved in assembling enough fissile material to produce a critical nuclear mass, cyber ‘weapons’, once developed, are very hard to retain.
Cyber ‘weapons’ are in fact just computer programs which can be pirated like any other. Since they are entirely comprised of information they can be copied quickly with no marginal cost.”
The release of the CIA’s Marble Framework and its use of obfuscation into the cold, hard light of day gives us a sense of why we should believe almost nothing that we hear about hacking. How can we be assured that the tracks that brought the U.S. intelligence services to the conclusion that the Russians hacked the 2016 election weren’t laid by the American intelligence services? The fact that the CIA is using languages of its foes around the world in its obfuscation framework should tell us all that we need to know.
Click HERE to read more from this author.
You can publish this article on your website as long as you provide a link back to this page.

Be the first to comment