Earlier this summer, the Electronic Frontier Foundation (EFF) released its annual assessment of major technology companies and how they protect your privacy. The report, entitled "Who Has Your Back?" looks at the privacy practices of various online service providers and how they handle government requests to access user data. The report examines the following five criteria:
1.) Industry-Accepted Best Practices: this measures companies on whether a company requires the government to obtain a warrant from a judge before handing over your online communications content, whether the company publishes a useful transparency report regarding how often the government sought user data and how often the company complied and whether the company publishes law enforcement guides explaining how they respond to data demands from the government.
2.) Tell users about government data requests: to earn a passing grade, internet companies must promise to tell users when the U.S. government seeks their data unless telling them is prohibited by law. This gives users prior notice so that they have a chance to challenge the request and defend themselves in court.
3.) Publicly disclose the company's data retention policies: to earn a passing grade, companies must disclose how long they maintain their data about their users, particularly data that is not accessible to the user including logs of users' IP addresses and deleted content.
4.) Tell users about government removal requests: Disclose the number of times governments seek the removal of user content or accounts and how often the company complies.
5.) Pro-user public policies opposing backdoors: EFF is asking companies to take a public position against the compelled inclusion of deliberate security weaknesses or other government-compelled back doors.
Of the 24 companies in the report, only 9 received a perfect score. These include Adobe, Apple, CREDO, Dropbox, Sonic, Wickr, Wikimedia, WordPress and Yahoo. Two of the poorest performers are major American telecoms; AT&T which received a passing grade in only one facet (industry-accepted best practices) and Verizon which received a passing grade in only two facets (industry accepted best practices and disclosure of the number of times that governments sought content removal).
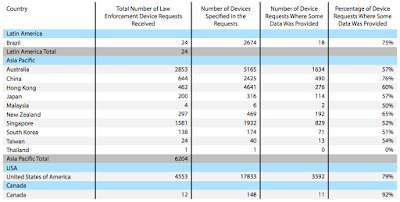
Let's put this into context by focus on Apple. Apple has appeared in EFF's annual report for five years running and it has adopted every best practice that EFF has defined as part of protecting consumers' privacy. In its latest transparency reportthat covers the period from July 1 to December 31, 2014, Apple reveals the following device requests:
The country with the most data requests was Germany with 7,478 law enforcement device requests covering 30,402 devices (i.e. iPhones, iPads, iPods and Macs) and that the country with the most total device requests was Poland where 30 law enforcement device requests covered a whopping 534,337 devices. In the case of Germany, some user data was provided to the government 57 percent of the time and in the case of Poland, some user data was provided to the government 60 percent of the time. Note that in the United States there were a total of 4,533 law enforcement device requests covering a total of 17,833 devices. Some user data was provided to the government for 3,592 or 79 percent of the requests.
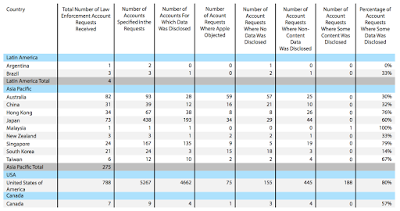
Here is a table showing the number of times that law enforcement requested account information from Apple between July and December 2014:
User account content that Apple can release includes iCloud emails, contacts, calendar information or Photo Stream content. In most cases, Apple will release only subscriber or transactional information not user content. By a very wide margin, the most law enforcement requests for account information took place in the United States with 788 requests covering 5,267 accounts. In 4,662 cases or 80 percent of total requests, Apple released some data to law enforcement. In only 155 cases was no data disclosed and in 75 cases or 9.5 percent of the total requests, Apple objected to the law enforcement request for information. Some user content as defined above was released in 188 cases or 23.9 percent of total law enforcement requests.
On the upside, for those of us that would rather not have our personal data follow us for an infinite length of time, Apple states that…
"Apple makes it easy for you to keep your personal information accurate, complete, and up to date. We will retain your personal information for the period necessary to fulfill the purposes outlined in this Privacy Policy unless a longer retention period is required or permitted by law."
Furthermore, according to a message from Tim Cook:
"Finally, I want to be absolutely clear that we have never worked with any government agency from any country to create a backdoor in any of our products or services. We have also never allowed access to our servers. And we never will."
As far as providing content such as mail logs, email content and subscriber information to law enforcement, Apple states that the following information is available from iCloud:
"i. Subscriber Information
When a customer sets up an iCloud account, basic subscriber information such as name, physical address, email address, and telephone number may be provided to Apple. Additionally, information regarding iCloud feature connections may also be available. iCloud subscriber information and connection logs with IP addresses can be obtained with a subpoena or greater legal process. Connection logs are retained up to 30 days.
ii. Mail Logs
Mail logs include records of incoming and outgoing communications such as time, date, sender email addresses, and recipient email addresses. Mail logs may be obtained with a court order under 18 U.S.C. § 2703(d) or a court order with an equivalent legal standard or a search warrant. iCloud mail logs are retained up to 60 days.
iii. Email Content
iCloud only stores the email a subscriber has elected to maintain in the account while the subscriber’s account remains active. Apple does not retain deleted content once it is cleared from Apple’s servers. Apple is unable to provide deleted content. Available email content may be provided in response to a search warrant issued upon a showing of probable cause.
iv. Other iCloud Content. Photo Stream, Docs, Contacts, Calendars, Bookmarks, iOS Device Backups
iCloud only stores content for the services that the subscriber has elected to maintain in the account while the subscriber’s account remains active. Apple does not retain deleted content once it is cleared from Apple’s servers. iCloud content may include stored photos, documents, contacts, calendars, bookmarks and iOS device backups. iOS device backups may include photos and videos in the users’ camera roll, device settings, app data, iMessage, SMS, and MMS messages and voicemail. iCloud content may be provided in response to a search warrant issued upon a showing of probable cause.” (my bold)
In closing, here's what Apple says about notifying users when their personal information is being sought by law enforcement:
“Apple will notify its customers when their personal information is being sought in response to legal process except where providing notice is prohibited by the legal process itself, by a court order Apple receives (e.g., an order under 18 U.S.C. §2705(b)), or by applicable law or where Apple, in its sole discretion, believes that providing notice could create a risk of injury or death to an identifiable individual or group of individuals, in situations where the case relates to child endangerment, or where notice is not applicable to the underlying facts of the case. “
It is interesting to note that Apple gets the highest grade from the Electronic Frontier Foundation when it comes to protecting our privacy, yet, it still provides both content and user information to law enforcement for a significant percentage of law enforcement requests. It makes one ponder what information is being provided to the government by the fifteen companies that didn't receive a perfect score on the EFF's annual assessment of the state of our privacy on the internet.
Click HERE to read more of Glen Asher's columns
You can publish this article on your website as long as you provide a link back to this page.



Be the first to comment