
Let’s open this posting by looking at the potential cyber threats against the United States from an early 2017 Defense Science Board document which examined, in detail, at America’s cyber vulnerabilities. It outlined three key challenges facing the United States ability to deter a cyber attack:
“1.) Major powers (e.g., Russia and China) form significant and increasing ability to hold U.S. critical infrastructure at risk or otherwise use the information domain to harm vital U.S. interests, and their more limited but growing capability to thwart our military response through cyber attack.;
2.) Lesser powers’(e.g., Iran and North Korea) and potentially non-state actors’ possible ability, through increasingly available cyber tools—indigenous, purchased, or transferred—to conduct catastrophic attacks on U.S. critical infrastructure.
3.) A range of state and non-state actors’growing capacity for persistent cyber attacks and costly cyber intrusions against the United States, which individually may be inconsequential (or be only one element of a broader campaign) but which cumulatively subject the Nation to a “death by 1,000 hacks.”
Thanks to the National Security Archive’s project on cyberwarfare, we have some inside information on how the United States security and intelligence infrastructure feels that one of the key threats, Iran, could (or already has) waged a cyberwar against the United States. In this posting, I will look at some of the documents that give us key information on this potential threat.
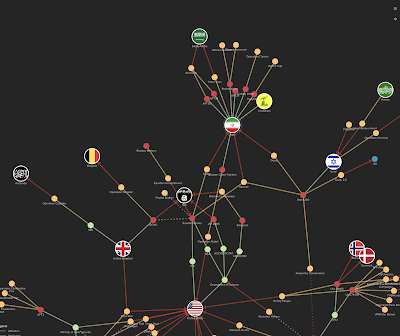
Let’s open with a graphic from the National Security Archive’s CyberWar map showing the links between various players in the cyberwarfare world and how they link to each other and ultimately both Iran (in the middle of the graphic) and the United States (at the bottom centre of the graphic):
Let’s look at the documents related to Iran’s possible links to a potential cyberwar with the United States:
1.) James Clapper (Director of National Intelligence) et al dated January 5, 2017 – Joint statement to the Senate Armed Services Committee on Foreign Cyber Threats to the United States:
“Tehran continues to leverage cyber espionage, propaganda, and attacks to support its security priorities, influence events and perceptions, and counter threats—including against U.S. allies in the Middle East. Iran has also used its cyber capabilities directly against the United States, as in distributed denial of service attacks in targeting the U.S. financial sector in 2012-13.”
The list of players in the cyberthreat arena in this statement also included Russia, China, North Korea, terrorist groups including ISIL, al-Qaeda and Hezbollah as well as the general criminal elements.
2.) Ilan Berman (Vice President American Foreign Policy Council) dated April 26, 2012 – Statement before the House of Representatives Committee on Homeland Security, Subcommittee on Cybersecurity, Infrastructure Protection and Security Technologies:
“Iran’s expanding exploitation of cyberspace can be attributed to two principal geopolitical drivers.
The first are the Iranian regime’s efforts to counter Western influence and prevent the emergence of a “soft revolution” within its borders. In his March 2012 Nowruz message to the Iranian people, President Obama alluded to the growing efforts of the Iranian regime to isolate its population from the outside world when he noted that an “electronic curtain has fallen around Iran.” That digital barrier has grown exponentially over the past three years, as Iran’s leadership has sought to quell domestic dissent and curtail the ability of its opponents to organize.
The proximate cause of this effort was the fraudulent June 2009 reelection of Mahmoud Ahmadinejad to the Iranian presidency, which catalyzed a groundswell of domestic opposition that became known colloquially as the “Green Movement.” In the months that followed, Iran’s various opposition elements relied extensively on the Internet and social networking tools to organize their efforts, communicate their messages to the outside world, and rally public opinion to their side. In turn, the Iranian regime utilized information and communication technologies extensively in its suppression of the protests—and thereafter has invested heavily in capabilities aimed at controlling the Internet and restricting the ability of Iranians to access the World-Wide Web.
The second geopolitical driver of Iran’s interest in cyberspace relates to the expanding conflict with the West over its nuclear ambitions. Since the Fall of 2009, Iran has suffered a series of sustained cyber attacks on its nuclear program. The most well-known of these is Stuxnet, the malicious computer worm that attacked the industrial control systems at several Iranian nuclear installations, including the uranium enrichment facility at Natanz, between late 2009 and late 2010. At the height of its effectiveness, Stuxnet is estimated to have taken ten percent or more of Iran’s 9,000 then-operational centrifuges offline.
Stuxnet has been followed by at least two other cyber attacks aimed at derailing Iran’s nuclear development. “Stars,” a software script targeting execution files, was uncovered by the Iranian regime in April 2011. Subsequently, “Duqu,” a malware similar to Stuxnet and aimed at gaining remote access to Iran’s nuclear systems, was identified in October/November 2011.”
Interestingly, Stuxnet appears to have been authored by either the United States (CIA) or Israel or a combination of the two, both of which have not confirmed their participation in the authorship of the cyberattack. For more information on Stuxnet, please click here.
According to his testimony, Mr. Berman asserts that Iran has launched a $1 billion government program to improve its cyber capabilities, both defensively and offensively and that Iran is now one of the most capable nations when it comes to its cyber-offence abilities.
Here is another quote:
“After all, it is not out of the question that the Iranian regime could attempt an unprovoked cyber attack on the United States. As the foiled October 2011 plot against Saudi Arabia’s ambassador to the United States indicates, Iran has grown significantly bolder in its foreign policy, and no longer can be relied upon to refrain from direct action in or against the U.S. homeland. Far more likely, however, is a cyberwarfare incident related to Iran’s nuclear program. In coming months, a range of scenarios—from a renewed diplomatic impasse to a further strengthening of economic sanctions to the use of military force against Iranian nuclear facilities—hold the potential to trigger an asymmetric retaliation from the Iranian regime aimed at vital U.S. infrastructure, with potentially devastating effects.
At the very least, it is clear that policymakers in Tehran are actively contemplating such an eventuality. Prudence dictates that their counterparts in Washington should be doing so as well.”
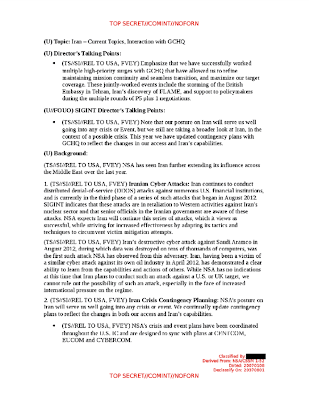
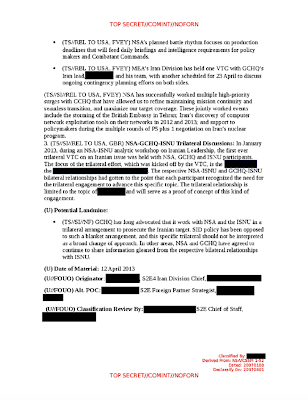
3.) Top Secret talking points prepared for a meeting between the director of the National Security Agency and the United Kingdom’s Government Communications Headquarters (GCHQ) which outlines Iran’s cyber attacks on Saudi Aramco and United States financial institutions:
Note that the talking points include a statement suggesting that Iran’s attacks against its foes may have been in retaliation for Western activities against Iran’s nuclear sector (i.e. Stuxnet).
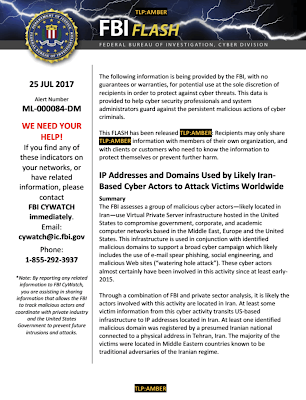
4.) FBI Flash alert dated July 25, 2017 outlining the use of American virtual private servers (i.e. VPNs) to compromise government, corporate and academic computer networks throughout the world:
Let’s close by going back to the Defence Science Board’s report, focusing on one of the key conclusions of the report:
“The United States must strengthen its cyber deterrence posture against these three critical challenges – and do so by focusing on the specific actors who pose these challenges. While progress is being made to reduce the pervasive cyber vulnerabilities of U.S. critical infrastructure, improvements are not on a pace to reduce risks to acceptable levels within the next decade. The introduction of massive numbers of digital sensors (the so-called Internet of Things), processors, and autonomous devices to today’s internet will only exacerbate an already tenuous posture and make defense even more challenging in the coming years. The unfortunate reality is that, for at least the coming five to ten years, the offensive cyber capabilities of our most capable potential adversaries are likely to far exceed the United States’ ability to defend and adequately strengthen the resilience of its critical infrastructures.”
The vulnerability of America’s vast infrastructure to outside cyber attacks should concern all of us given that so much of our daily lives depend on that infrastructure. Without it, we could find ourselves forced to live a much more primitive existence.
Click HERE to read more from this author.
You can publish this article on your website as long as you provide a link back to this page.

Be the first to comment